Overview
Cloud architecture design has become a leadership issue, not just an engineering one. As environments grow across public cloud, private infrastructure, and AI-driven workloads, architecture decisions now shape cost control, security posture, delivery speed, and long-term resilience at the business level. This is also why cloud architecture in cloud DevOps has become more important, as infrastructure choices now directly affect how teams build, release, secure, and operate modern platforms.
This article explains what strong cloud architecture looks like in 2026 and where teams most often get it wrong. It covers the core decisions behind scalable, secure platforms, including workload design, networking, identity, data protection, reliability, and governance. It also looks at the tradeoffs between containers, serverless, and managed PaaS, along with the operational patterns that help modern cloud environments stay efficient as they grow. A well-planned cloud server architecture also plays a central role in supporting performance, uptime, and cost-efficient infrastructure operations.
By the end, you will have a clearer framework for evaluating your current architecture, identifying common gaps, and planning the next steps to modernize your platform with more confidence.
Why Thoughtful Design of Cloud Architecture Matters More Than Ever
Cloud spending keeps rising. Global public cloud end-user spending was projected to reach $723.4 billion in 2025, but cost alone does not tell the whole story.
More workloads now need to meet regional data-sovereignty requirements, AI workloads introduce sudden compute-intensive spikes, and customers increasingly expect near-zero downtime. Cost still matters, but it is no longer the only pressure shaping architecture decisions.
When architecture decisions are left to chance, the result is usually a mix of rising costs, inconsistent security controls, and slower delivery as teams keep rebuilding platform foundations instead of reusing them.
Purposeful design addresses these risks upfront, turning the cloud into a strategic asset instead of an uncontrolled expense.
A leading provider of managed IT services often starts client engagements with an architecture assessment that maps technical gaps to business risk. Whether you use an external partner or internal architects, the principle is identical: diagnose before you build.
Common Challenges We See in Client Environments
Many client environments do not have one dramatic architectural flaw. The bigger issue is usually the accumulation of smaller gaps that were never addressed early enough. Over time, those gaps start to slow delivery, increase operational risk, and make cloud costs harder to control.
Some of the most common problems we see include:
-
no standardized landing zone, so each team ends up building in a slightly different way
-
manual infrastructure provisioning, which slows down delivery and creates unnecessary room for human error
-
weak IAM and secrets management, with access that is broader and less controlled than it should be
-
limited visibility into cloud costs, making overspend harder to detect before it becomes a bigger issue
-
no clear rollback strategy in deployments, which increases delivery risk when releases go wrong
-
development and operations teams working in silos, leading to friction, duplicated effort, and inconsistent ownership
-
cloud resources being deployed without enough governance, creating policy gaps and long-term control issues
-
difficult migration from on-premises environments, especially when legacy systems and dependencies were never properly mapped
In most cases, these problems do not appear separately. They compound. Manual provisioning leads to drift. Weak governance makes cloud sprawl harder to control. Poor cost visibility hides architectural inefficiencies until they become expensive. This is why architecture work should start with the practical issues already slowing the environment down, not just with an ideal target-state diagram.
Defining Cloud Architecture Design for 2026
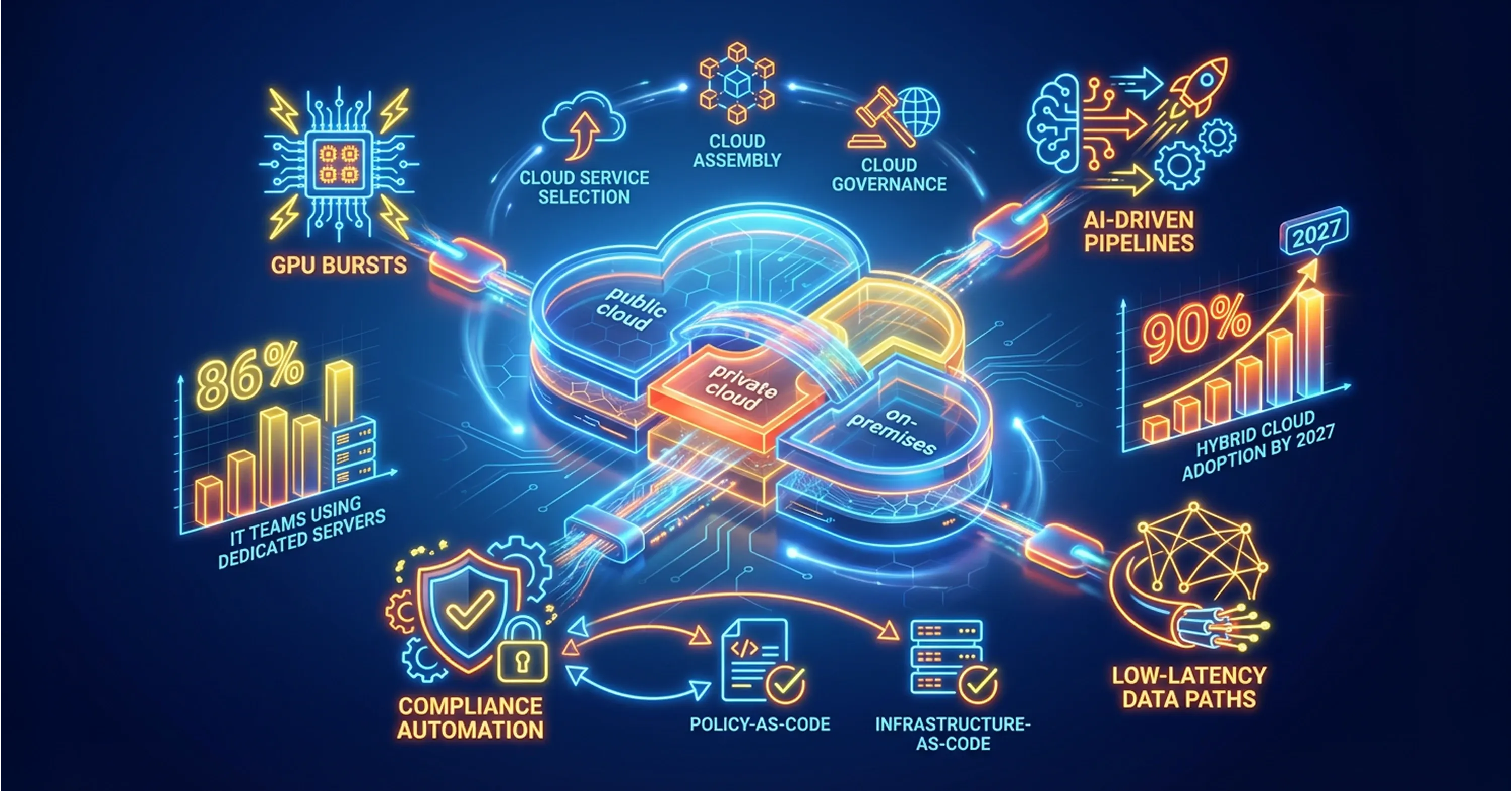
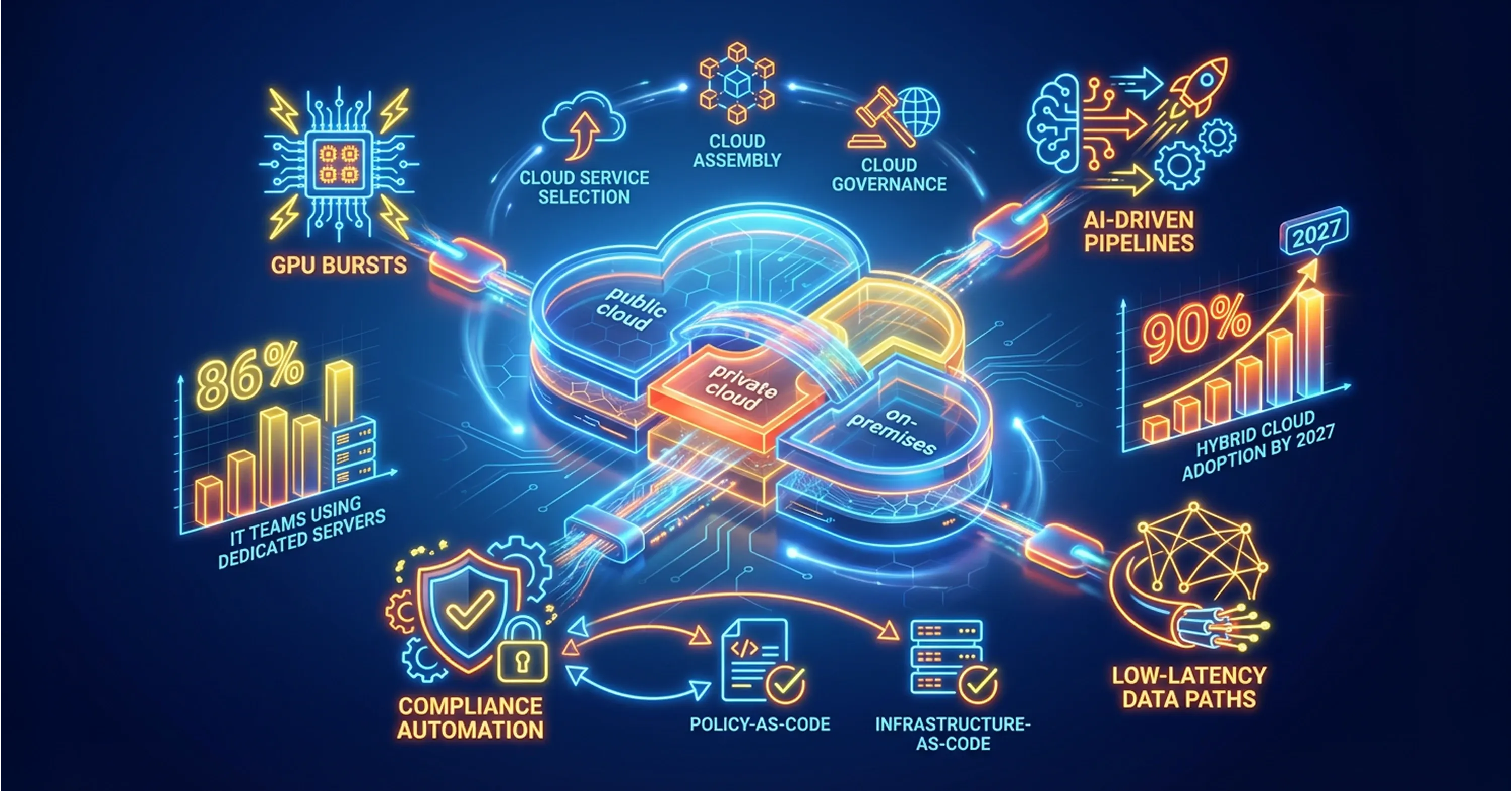
Cloud architecture design is the structured approach to selecting, assembling, and governing cloud services - compute, storage, network, and platform components - so that they meet business objectives at scale. By 2026, three shifts redefine what “good” looks like:
-
Hybrid is the default. 90% of organizations will run hybrid clouds by 2027 blending public, private, and on-prem resources, including dedicated servers still used by 86% of IT teams.
-
Architecture must support AI-driven pipelines, which demand GPU bursts and low-latency data paths.
-
Policy-as-code and Infrastructure-as-Code (IaC) automate compliance from the first commit, not during audits.
Therefore, design now spans both the control plane (governance, IAM, policies) and the data plane (traffic flow, services, storage classes) across multiple execution venues.
For a broader review of how intentional design outpaces accidental environments, see the approach and pitfalls in Multi-Cloud Strategy: Building a Winning Cloud Strategy for 2026 and Beyond.
These shifts shape the architecture decisions that matter most in practice.
Key Architectural Decisions You Cannot Ignore
Cloud architecture usually does not fail because teams ignore the obvious. It fails when one important decision is treated as secondary until it turns into a security gap, a reliability issue, or a cost problem. A platform may scale well but remain difficult to govern. It may be secure on paper but hard to recover during an outage. That is why architecture decisions need to work together as one system.
In practice, six areas shape whether a cloud environment remains secure, scalable, and manageable over time.
1. Workload Patterns
The first decision is about fit. Some workloads benefit from containers because they need portability and control. Others work better in serverless environments, especially when demand is event-driven or unpredictable. Managed PaaS can be the right choice when speed and lower operational overhead matter most.
The goal is not to force one model everywhere, but to match the right execution model to the workload.
Modern teams often get the best results by combining these approaches across the application lifecycle. For more on how these delivery models work together, see Top Cloud Sources Every Business Should Know.
2. Networking and Segmentation
Networking shapes how traffic moves and how safely systems interact. Strong architectures separate public, application, and data layers clearly, while using models such as hub-and-spoke or shared VPCs to keep routing and control manageable.
Zero-trust principles also matter here. Requests should be verified by policy, not trusted by default because they come from inside the environment.
3. Identity and Access Control
Identity is one of the most important layers in any cloud environment. In mature architectures, access is tied to a central identity provider, permissions are kept narrow, and credentials are rotated automatically.
When identity is inconsistent, every other security control becomes harder to trust.
4. Data Protection and Residency
Data decisions affect more than storage. They shape compliance, resilience, and customer trust. Sensitive data should be encrypted in transit and at rest, classified correctly, and stored in ways that respect residency and regulatory requirements.
This is one of the easiest areas to underestimate early and one of the hardest to fix later.
5. Reliability and Disaster Recovery
Reliability should reflect business impact, not just technical ambition. Critical systems need clear recovery targets, resilient deployment patterns, and failover plans that are tested before incidents happen.
The more important the service, the less room there is for untested assumptions.
6. Observability and Incident Readiness
Teams cannot manage what they cannot see. Strong observability means centralized logs, metrics, and traces, combined with alerting, runbooks, and clear ownership during incidents.
For more on aligning monitoring with operational outcomes, see CI/CD Monitoring: Continuous Monitoring for Performance, Security, and Compliance.
Across all six areas, governance ties everything together. Infrastructure-as-Code, policy-as-code, and budget guardrails help prevent drift as the environment grows.
Designing across these domains becomes especially complex in hybrid environments or AI-heavy platforms. If you want expert guidance, you can book a cloud architecture consultation to review your current platform and identify the most impactful improvements.
Choosing the Right Workload Pattern: Containers, Serverless, or Managed PaaS?
Choosing between containers, serverless, and managed PaaS depends on the workload itself - not on trends. The right model depends on performance needs, compliance requirements, operational complexity, and how much control the team needs.
Containers are a strong fit for workloads that need portability, custom runtimes, and deeper control. Serverless works well for event-driven or unpredictable workloads, especially when reducing idle cost matters. Managed PaaS is often the best option when teams want to move faster and reduce operational overhead, even if that means giving up some flexibility.
In practice, most organizations do not need one model everywhere. They need the right fit for each workload. As a rule of thumb, containers suit control and portability, serverless fits bursty event-driven execution, and managed PaaS works well for standardized services such as databases, messaging, or inference endpoints.
Each decision should still be validated with a proof of concept and a realistic cost model. Remember that 42% of IT teams reported moving workloads back to dedicated servers when public cloud bills exceeded early expectations. A reversible path usually creates fewer problems later.
If your team is evaluating containers, serverless, or managed services and wants to avoid costly architectural mistakes, you can schedule a cloud architecture consultation to review your workloads and determine the most suitable platform strategy.
For deeper exploration of deployment tradeoffs and modern orchestration tools, see Containerization and Orchestration Tools for Simplifying Modern Application Deployment.
Choosing the Right Cloud Architecture Pattern
A fintech startup launched with serverless functions but hit concurrency limits during peak trading hours. A hybrid approach now runs critical pricing engines in container clusters while peripheral jobs remain serverless, cutting latency from 700 ms to 90 ms. With deployment models in place, let us piece together the full blueprint.
The Modern Cloud Architecture Blueprint
A modern cloud architecture should give teams a stable foundation without making the platform harder to operate as it grows. In most environments, that starts with a landing zone that centralizes identity, logging, billing, and shared networking controls. This creates consistency early and reduces the risk of every team building its own version of the platform.
On top of that foundation sits the application layer, where microservices, APIs, and event-driven services need to run in a way that supports both scale and operational control. In many cases, this includes Kubernetes for containerized workloads and an event bus for asynchronous communication between services.
The data layer should be designed for both resilience and flexibility. Managed relational databases, object storage with lifecycle policies, and cloud-based analytics platforms help organizations support operational workloads and reporting without adding unnecessary infrastructure overhead.
For organizations running AI workloads, the architecture also needs to account for GPU-intensive processing, controlled access to data assets, and secure support for model training or inference pipelines. Just as important, the entire environment should be backed by a strong observability layer, with centralized metrics, logs, traces, and alerting tied into incident response workflows.
For a practical breakdown of how next-generation platforms support elasticity and hybrid operations, review Be Cloud: The Next-Gen Platform for Scalable Business.
Avoiding the Pitfalls: Common Failure Patterns
Most architecture problems do not begin with a dramatic outage. They usually appear earlier as weak access controls, fragile deployment patterns, limited observability, delayed patching, or poor cost discipline. These issues often stay manageable for a while, then become much harder to fix as the environment grows.
Common warning signs include over-permissioned IAM roles, single-region dependencies in critical systems, siloed logging that slows incident response, manual patching processes, and budget alerts that are only noticed after overspend has already happened. The safest approach is to build security, observability, and cost controls into the platform from the start rather than trying to bolt them on later.
For a security-oriented blueprint blending compliance, automation, and DevSecOps in cloud environments, read Balancing Cloud Computing and Cloud Security: Best Practices.
From Vision to Reality: An Implementation Roadmap
A phased approach lets teams deliver value while iterating.
-
Baseline Assessment
-
Discover current assets, shadow IT, and spend.
-
Map findings to the six decision domains.
-
Foundation
-
Minimum Viable Platform
-
Workload Migration
-
Optimization
-
Right-size compute, add autoscaling, enforce budgets.
-
Run chaos experiments to validate resilience.
-
Expansion and Continuous Improvement
-
Introduce AI workloads, advanced data pipelines.
-
Automate security posture checks and governance audits.
For a foundational roadmap and the differences between infrastructure and architecture, see What Is Cloud Infrastructure? A Beginner’s Guide to Cloud Computing.
If internal bandwidth is limited, working with an experienced managed IT services partner can accelerate the first stages of platform design and implementation, while allowing internal teams to stay focused on higher-value engineering work.
Start with a Cloud Architecture Assessment
Many cloud environments evolve organically over time, which often leads to hidden complexity, security gaps, and unnecessary infrastructure costs. A structured cloud architecture assessment helps organizations evaluate their current environment across key domains such as networking, identity management, data protection, reliability, and governance.
During an architecture assessment, experts typically analyze infrastructure configuration, workload patterns, and operational processes to identify risks and optimization opportunities. The result is a clear modernization roadmap aligned with business priorities and technical constraints.
If you are considering a modernization initiative or planning to scale AI workloads, starting with an architecture assessment can significantly reduce implementation risk.
For organizations handling sensitive infrastructure information, these discussions are typically conducted under a mutual Non-Disclosure Agreement (NDA) to ensure full confidentiality when reviewing architecture diagrams, security configurations, and operational practices.
Measuring Success: Business Outcomes and Metrics
Outcomes trump diagrams. Track these signals:
-
Customer-visible uptime (SLA vs SLO adherence).
-
Mean time to recovery (MTTR) during incidents.
-
Deployment frequency and lead time for changes.
-
Cloud spend per customer transaction.
-
Security findings closed within target windows.
-
Compliance audit pass rates.
To drill down on how to measure cloud migration effectiveness, automate tracking, and translate engineering success into business terms, see How to Build a Cloud Services Support Model That Scales.
Tie each metric to executive priorities: revenue protection, risk reduction, or speed of innovation. When cloud computing is projected to hit $ 781.27 billion, the stakes justify disciplined measurement.
Conclusion
Cloud architecture design is no longer a sideline concern. It is the blueprint that keeps growth sustainable, secures data, and gives teams the foundation they need to move faster with confidence. In modern engineering environments, cloud architecture in cloud DevOps plays a central role in connecting infrastructure automation, application delivery, and governance into a more consistent operating model.
At the same time, a well-designed cloud server architecture helps compute, networking, and storage scale reliably without sacrificing security, performance, or cost control.
By working through the six decision domains, selecting the right workload patterns, and following a disciplined roadmap, CTOs and DevOps leaders can build platforms that are secure, scalable, and ready for 2026 and beyond.