How Cloud Security Evolved from Add-On to Foundation
For years, security was treated as a final checkpoint. Teams would design infrastructure, deploy workloads, and then call in a security review. That model worked when most systems lived in a single data center with a well-defined perimeter. Cloud changed everything.
As organizations moved critical systems, sensitive data, and customer-facing applications into cloud environments, the old perimeter disappeared. Security could no longer sit at the edge. It had to be embedded into infrastructure design, DevOps workflows, and daily operations. This shift turned cloud security into something structural, not supplemental. If you want to understand the risks of piecemeal digital foundations and how to avoid them, see The Danger of the 'Franken-Stack': Why Patchwork IT Will Kill Your Growth and How to Build a Secure, Scalable Foundation.
Today, identity is the primary control layer. Who can access what, under which conditions, and with how much privilege - these decisions define the security posture of a cloud environment more than any perimeter control.
Built around that identity layer, modern cloud security operates across: network segmentation and lateral movement controls, workload protection across VMs, containers, and serverless functions, data encryption in transit and at rest, API security governing service-to-service communication, compliance enforcement tied to regulatory frameworks, and continuous monitoring for real-time anomaly detection.
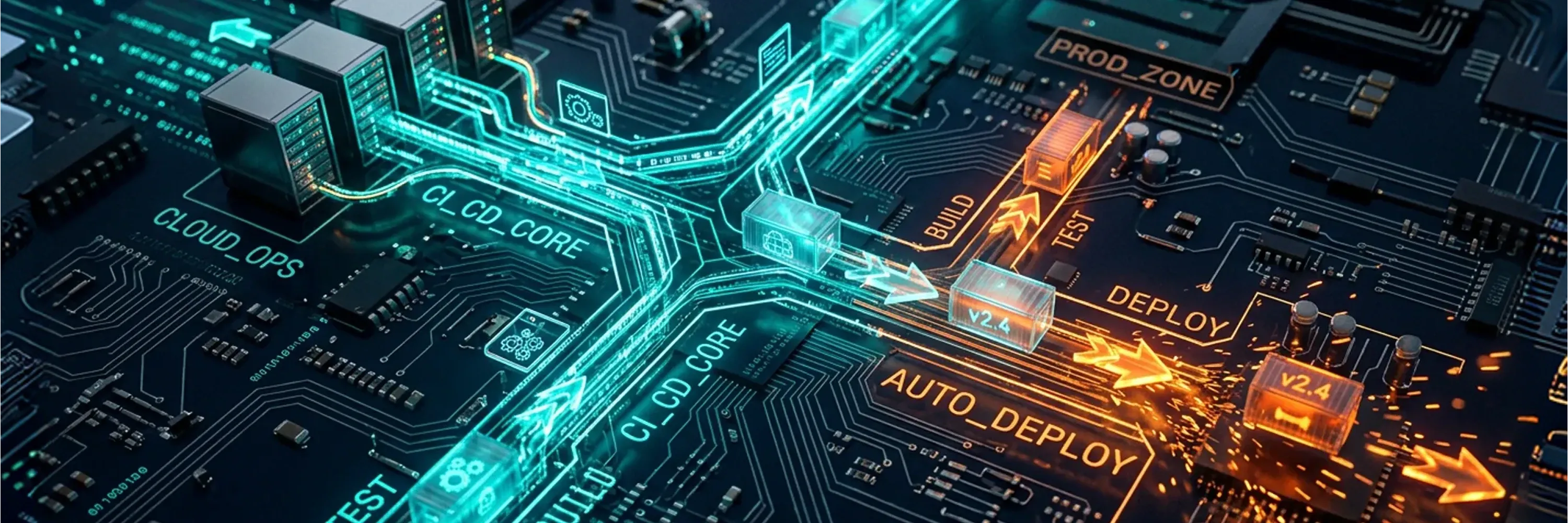
Phrases like policy-as-code, continuous control validation, and secure-by-default platforms are not buzzwords. They describe how mature teams operationalize these controls - embedded into pipelines, not reviewed after the fact.
Why Security Must Be Built In, Not Added Later
Consider a financial services company migrating its core banking platform to a hybrid cloud. Rather than adding firewall rules after deployment, the team embedded IAM policies, encryption standards, and network segmentation directly into the infrastructure-as-code templates. When a misconfigured access rule was introduced during a sprint, automated policy checks caught it before deployment. Security did not slow the release cycle. It prevented a potential breach before it started.
This evolution from add-on to foundation reflects a broader reality: organizations increasingly rely on secure cloud environments to run critical systems, manage sensitive data, support distributed teams, and maintain uptime. Security is no longer separate from infrastructure. It is infrastructure.
What Is Driving This Shift Toward Security-First Cloud Architecture?
Understanding why cloud security became foundational requires looking at the forces pushing organizations in this direction. These are not theoretical risks. They are operational realities that affect performance, resilience, governance, and business continuity every day.
The adoption of hybrid and multi-cloud strategies has expanded the attack surface significantly. When workloads run across multiple providers and on-premises systems, visibility becomes fragmented. Misconfigurations, which remain one of the most common causes of cloud breaches, multiply across environments. Overprivileged access, where users or services have more permissions than they need, creates openings that attackers are quick to exploit.
Remote and distributed access adds another layer of complexity. Employees, contractors, and partners connect from different locations and devices. Every connection point is a potential entry for compromise if it is not governed by consistent security policies.
At the same time, compliance requirements continue to grow. Regulations around data residency, privacy, and sovereignty demand that organizations know exactly where their data lives and who can access it. 17% of survey respondents are currently investing in sovereign cloud solutions and over half (53%) plan to invest, a clear sign that data control and regulatory alignment are shaping cloud decisions.
The drivers behind sovereign cloud adoption reinforce this point. The most important factors are cybersecurity and data control (61%), customer confidence and trust (40%), and compliance with national policies and regulation (39%). These numbers show that security is not just a technical concern. It is a trust and governance issue.
For organizations navigating these pressures, see how a unified security strategy for cloud and hybrid environments helps reduce visibility gaps, enforce consistent policies, and streamline compliance across complex estates.
How Security-First Architecture Strengthens Cloud Operations
When security is embedded from the start, teams spend less time responding to incidents and more time shipping. Detection is faster because controls are already instrumented. Remediation is more precise because the blast radius of any failure is contained by design. This is where the idea of cloud security as the IT backbone becomes most tangible.
Several practical approaches define this architecture:
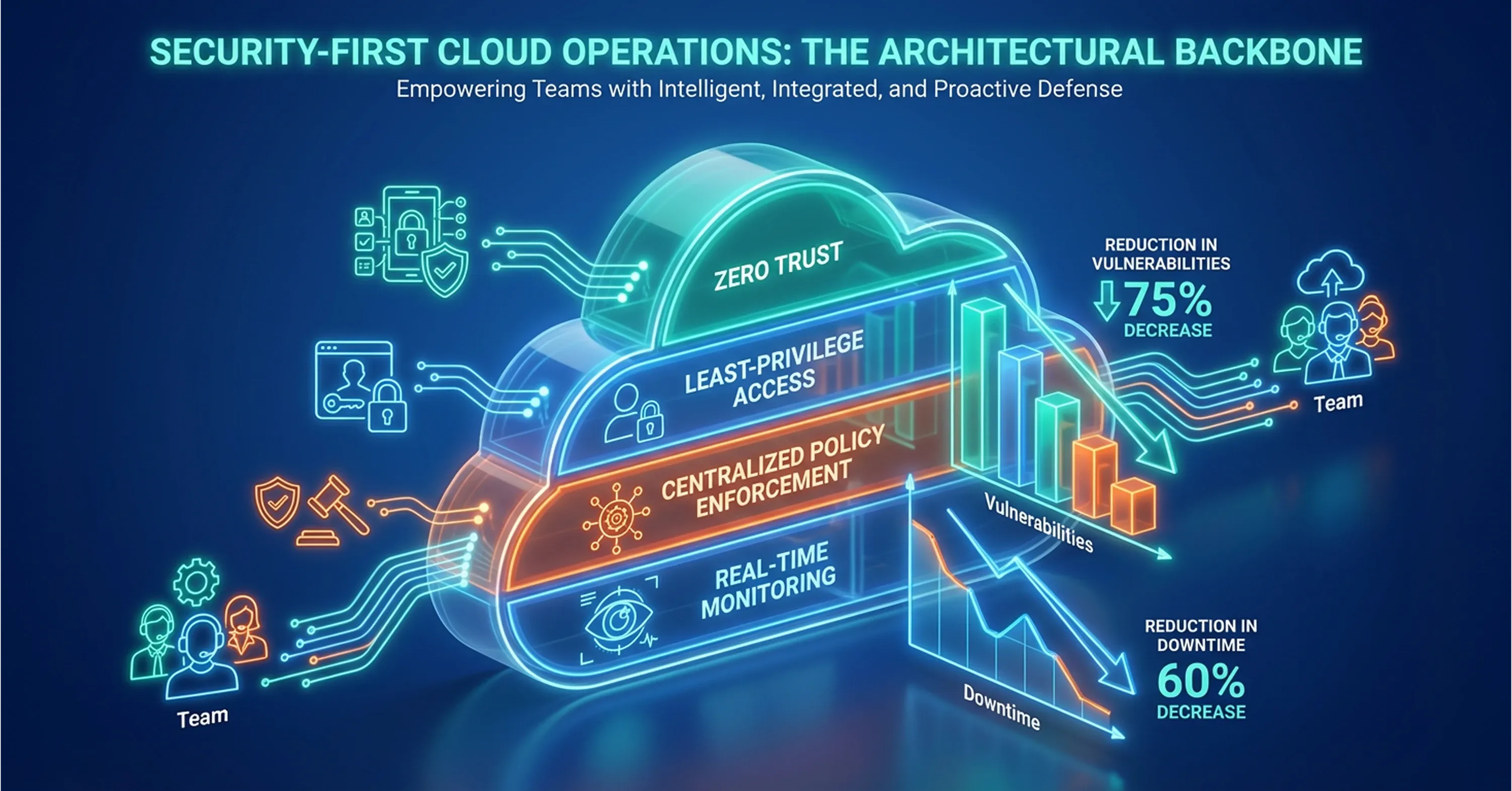
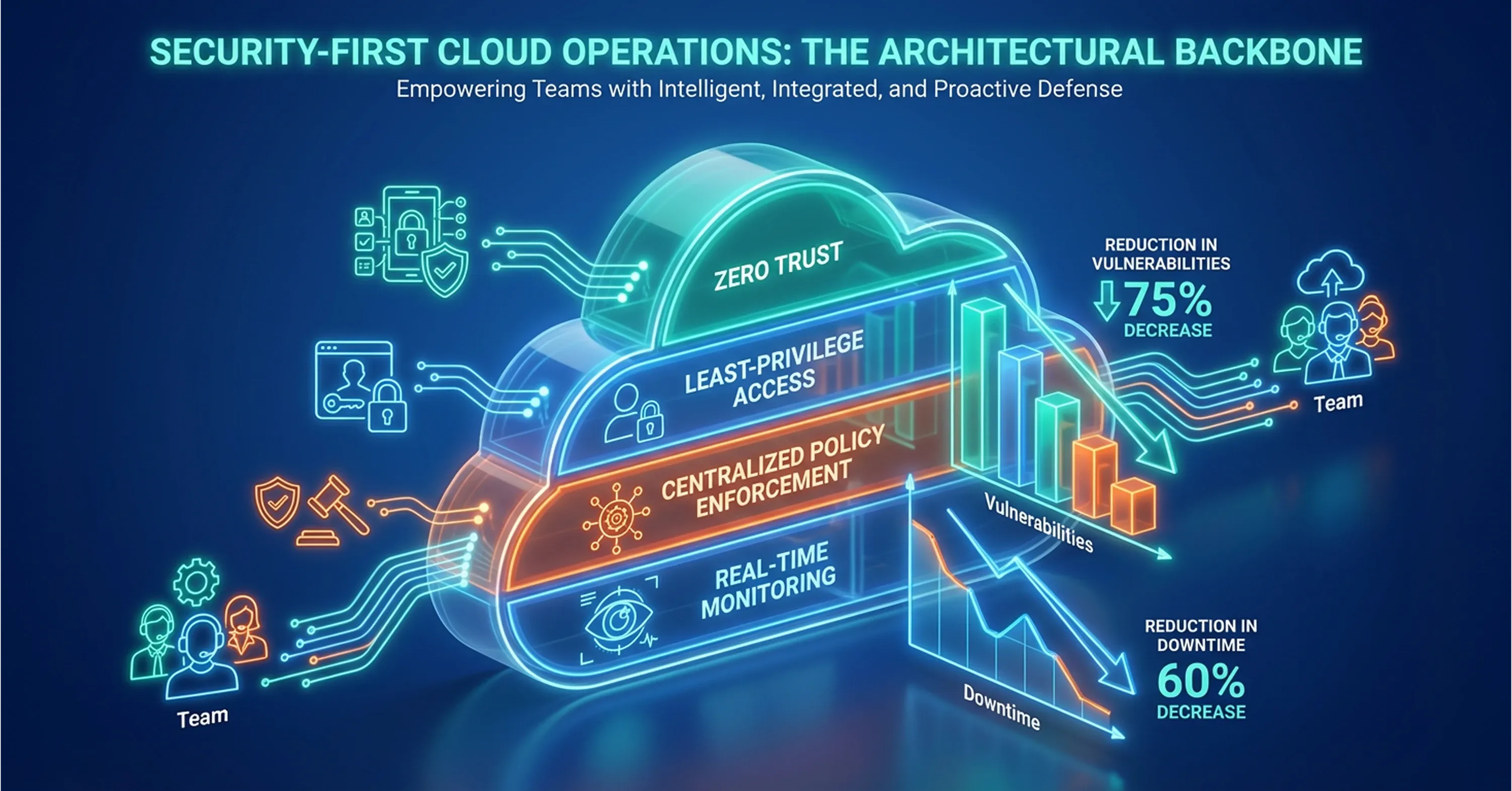
-
Zero trust, a model that assumes no user or device is trusted by default and requires continuous verification
-
Least-privilege access, which limits permissions to only what is needed for a specific task or role
-
Centralized policy enforcement, ensuring consistent rules across all environments regardless of provider
-
Real-time monitoring and observability, which combines logs, metrics, and traces to detect threats and performance issues simultaneously
These are not abstract frameworks. They are operational strategies that affect how teams build, deploy, and manage cloud systems every day. For a deep dive into how these controls come together, explore the Cloud Managed Security: Unified Security Strategy for Cloud and Hybrid Enviroinments.
Cloud is the top cybersecurity threat organizations feel least prepared to manage, which makes the case for security-first design even more urgent. Organizations that wait to address security after deployment consistently find themselves responding to incidents they could have prevented.
Why Cloud Security Is Now a Business and Budget Priority
The shift is not just architectural. It is financial and strategic. Decision-makers across industries now rank cloud security among their highest investment priorities, reflecting its role as core infrastructure rather than a cost center.
AI and cloud security are the top two cyber budget priorities for the year ahead, signaling that leadership teams see these areas as essential to maintaining operations, not just avoiding risk. This budgetary focus aligns with a broader shift in how organizations evaluate their technology partners and providers.
When selecting telco and technology providers, security is the top attribute that businesses look for. This means that cloud security posture now influences procurement decisions, partner evaluations, and vendor contracts. It is not a background concern. It is a deciding factor.
For IT leaders, cloud architects, and CTOs, this translates into clear expectations:
-
Security must be measurable, auditable, and visible across all cloud environments
-
Governance and compliance capabilities must be built into the cloud platform, not managed through separate tools
-
Incident detection and response must operate continuously, not on a scheduled basis
-
Security controls must scale with the infrastructure, not become a bottleneck during growth
Organizations that align their cloud strategy with these expectations gain a competitive advantage. They can move faster because security does not slow them down. They can meet regulatory requirements without rearchitecting. And they retain customer trust because their data governance is provable, not just promised.
For actionable steps on balancing cloud innovation with strong security and governance, read Balancing Cloud Computing and Cloud Security: Best Practices.
Why Integrated Cloud Security Has Become a Strategic Advantage
A logistics firm undergoing digital transformation chose its cloud provider based primarily on built-in security capabilities, including native encryption, automated compliance reporting, and integrated identity management. This decision reduced its time to achieve SOC 2 compliance by several months and allowed the IT team to focus on application performance rather than patching security gaps after the fact.
This is why managed services partners like ABS Technologies are playing a bigger role in modern cloud operations. ABS Technologies positions its services around cloud infrastructure management, DevOps automation, security, and real-time monitoring, helping organizations build and operate cloud environments with a more integrated approach. For teams working across hybrid or multi-cloud environments, that kind of support can turn cloud security from a separate concern into a stronger operational foundation.
What Organizations Usually Get Wrong
Most cloud security failures are not sophisticated attacks. They are operational gaps that accumulate over time.
The most common: overprivileged IAM, where users and services hold far more access than their role requires. Exposed storage buckets misconfigured during rapid deployment. Weak key management that treats encryption as a formality. Alert fatigue from fragmented tooling that produces noise instead of signal. And the most dangerous assumption - that native cloud provider controls constitute a complete security posture.
They do not. Native controls are a starting point. Governance, validation, and continuous enforcement are what turn them into actual protection.
How to Measure Cloud Security Maturity
Security without measurement is posture theater. The metrics that indicate real maturity: policy violation rate, IAM hygiene score, mean time to detect (MTTD), mean time to respond (MTTR), encryption coverage across workloads, control drift frequency, and audit readiness at any given point.
Organizations that track these consistently can demonstrate security posture to leadership, auditors, and partners - not just claim it.
Day-Two Operations: What Happens After Deployment
Security-first architecture does not end at launch. Day-two operations - configuration drift management, ongoing access review, incident triage, posture management, and control validation over time - determine whether a secure foundation stays secure.
Most organizations invest heavily in initial deployment and underinvest in what comes after. Drift is silent. Permissions accumulate. Controls erode. Without active day-two discipline, a well-architected environment degrades faster than most teams expect.
The Trade-Offs Worth Acknowledging
Multi-cloud flexibility comes with governance overhead. Every additional provider is another control plane to manage, another policy set to maintain, another audit scope to cover. Done poorly, multi-cloud creates fragmentation that weakens visibility rather than strengthening it.
The honest calculus: more cloud environments mean more surface area. Security strategy needs to account for that complexity upfront - not absorb it reactively.
Why Is Cloud Security the New IT Backbone?
Cloud security has become the foundational layer of modern IT infrastructure because organizations now depend on secure cloud environments to run critical systems, manage sensitive data, support remote operations, and maintain uptime. Security is no longer added after deployment. It is embedded into infrastructure design, DevOps workflows, and daily operations. Key approaches include zero trust, least-privilege access, centralized policy enforcement, and continuous monitoring across hybrid and multi-cloud environments.
Conclusion
Cloud security is no longer a feature you evaluate separately from your infrastructure. It is the layer that determines whether your infrastructure can perform, scale, and recover when it matters most. The shift from add-on to backbone reflects real operational demands: expanding attack surfaces, distributed teams, regulatory complexity, and the need for consistent governance across multiple cloud environments.
Organizations that embed security into their cloud architecture from the start gain more than protection. They gain speed, resilience, and the confidence to grow without compromising stability. For IT leaders and technical decision-makers navigating hybrid and multi-cloud realities, treating cloud security as foundational is no longer forward-thinking. It is simply how modern infrastructure works.
For further guidance on building your organization’s cloud backbone, consider reviewing ABS Technologies’ resources on managed IT and cloud security strategies.