Overview
We will start with the short history of IaC, then examine the new bottleneck - managing thousands of templates and the drift they create. From there, we build a narrative that shows why GitOps is the missing bridge between sprawl and self-healing. You will see how policy, observability, and disaster recovery now live “as code,” and how large language models (LLMs) are already refactoring legacy CloudFormation or ARM into reusable Terraform modules.
By the end, you will know:
-
The lifecycle every IaC stack should follow
-
How to detect and fix drift automatically
-
Where AI SREs fit and what they can realistically do today
-
Practical steps to embed governance, cost controls, and resilience into every pull request
From Shell Scripts to Declarative IaC Tools
The early 2010s were dominated by ad-hoc Bash and PowerShell scripts that spun up virtual machines. Those scripts were brittle, environment-specific, and nearly impossible to audit.
Today, declarative iac tools such as Terraform, Pulumi, and OpenTofu describe the desired end state instead of the sequence of commands.
This shift has:
-
Reduced human error by codifying intent
-
Enabled peer reviews and automated testing through Git
-
Accelerated deployments: reached USD 759.1 million in 2025, with analysts projecting a 20.3% CAGR at the time of the report.
Yet the move to code introduced its own pain: hundreds of templates, each diverging over time.
The key takeaway: provisioning is solved, but lifecycle management still is not. Next we address that gap.
How Template Duplication Amplifies Risk and Slows Security Patching
A retail fintech used hundreds of CloudFormation stacks. When a core VPC template needed a security patch, teams discovered 23 hand-edited copies. A one-line fix became a month-long audit. Switching to a single Terraform module stored in Git cut patch time to 30 minutes.
Confronting IaC Sprawl and Configuration Drift
Even declarative files drift when engineers change resources directly in the console, bypassing code. Over months, the “declared” and “actual” states diverge, making compliance reports meaningless.
Start by mapping the sprawl:
-
Inventory all repositories, templates, and modules
-
Tag ownership and business impact
-
Identify duplicates and abandonware
Then deploy drift-detection tools that compare state files to live cloud APIs. Popular choices include built-in drift detection using terraform plan, AWS Config, Firefly, or custom scripts.
To resolve drift automatically:
-
Run detections on a schedule (hourly for critical stacks)
-
Send pull requests that reconcile differences instead of applying changes silently
-
Route approvals to the stack owner with context and cost impact
Finish with dashboards that show “drift debt” trending down.
The result: teams regain confidence that code is truth and can move on to higher-value work.
Hourly Drift Detection Uncovered 700 Misconfigurations in a Week
A European telco enabled hourly drift scans on 2 000 AWS accounts. In the first week, 700 misaligned resources surfaced, including a public S3 bucket. Automated pull requests corrected 93% within 48 hours, saving an estimated EUR 120 000 in audit effort. For a deeper dive into how automation, environment consistency, and DevOps-driven remediation address drift, see From Code to Customer: Accelerating Innovation with Cloud DevOps.
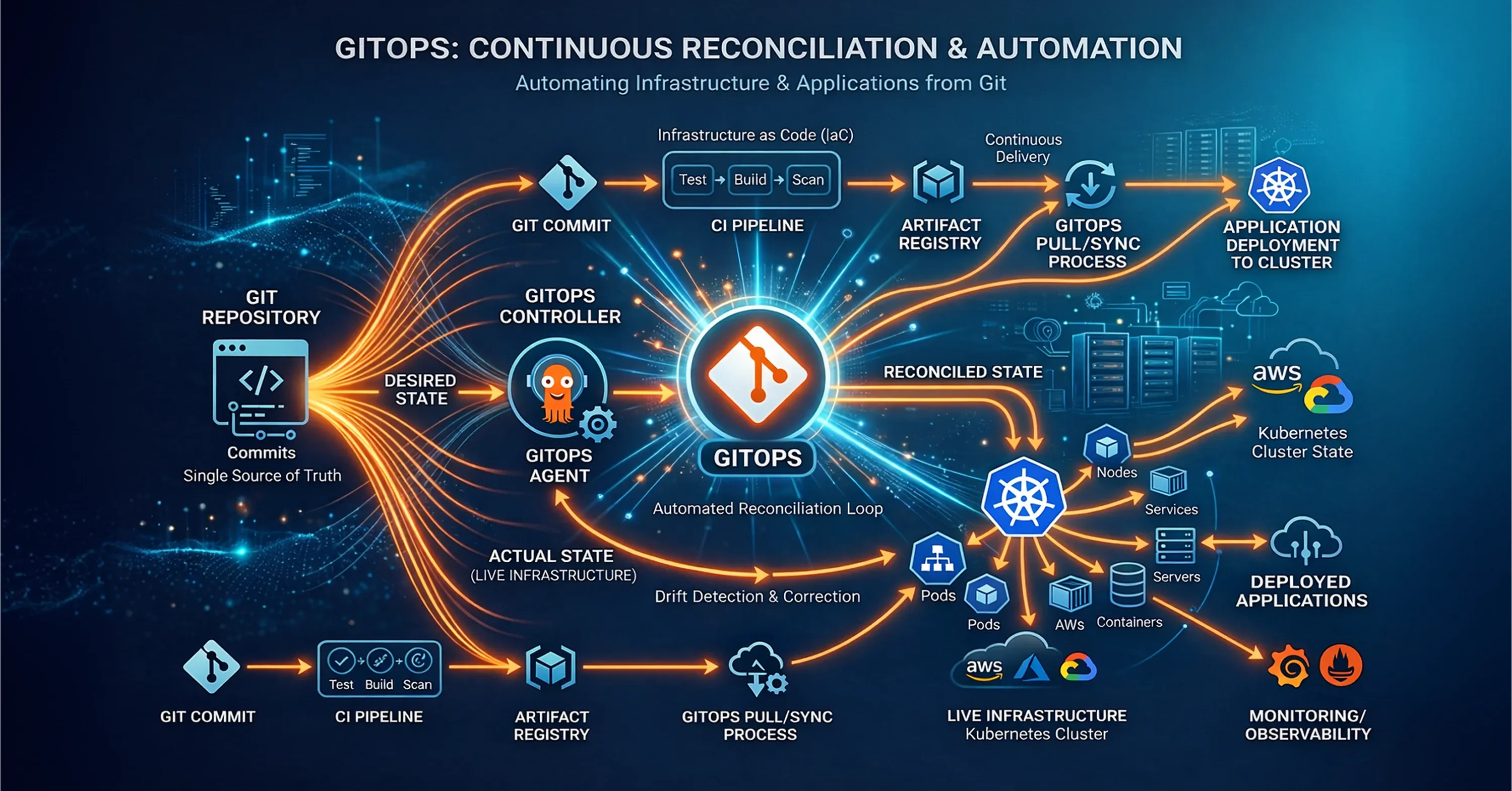
GitOps: The State Reconciliation Engine
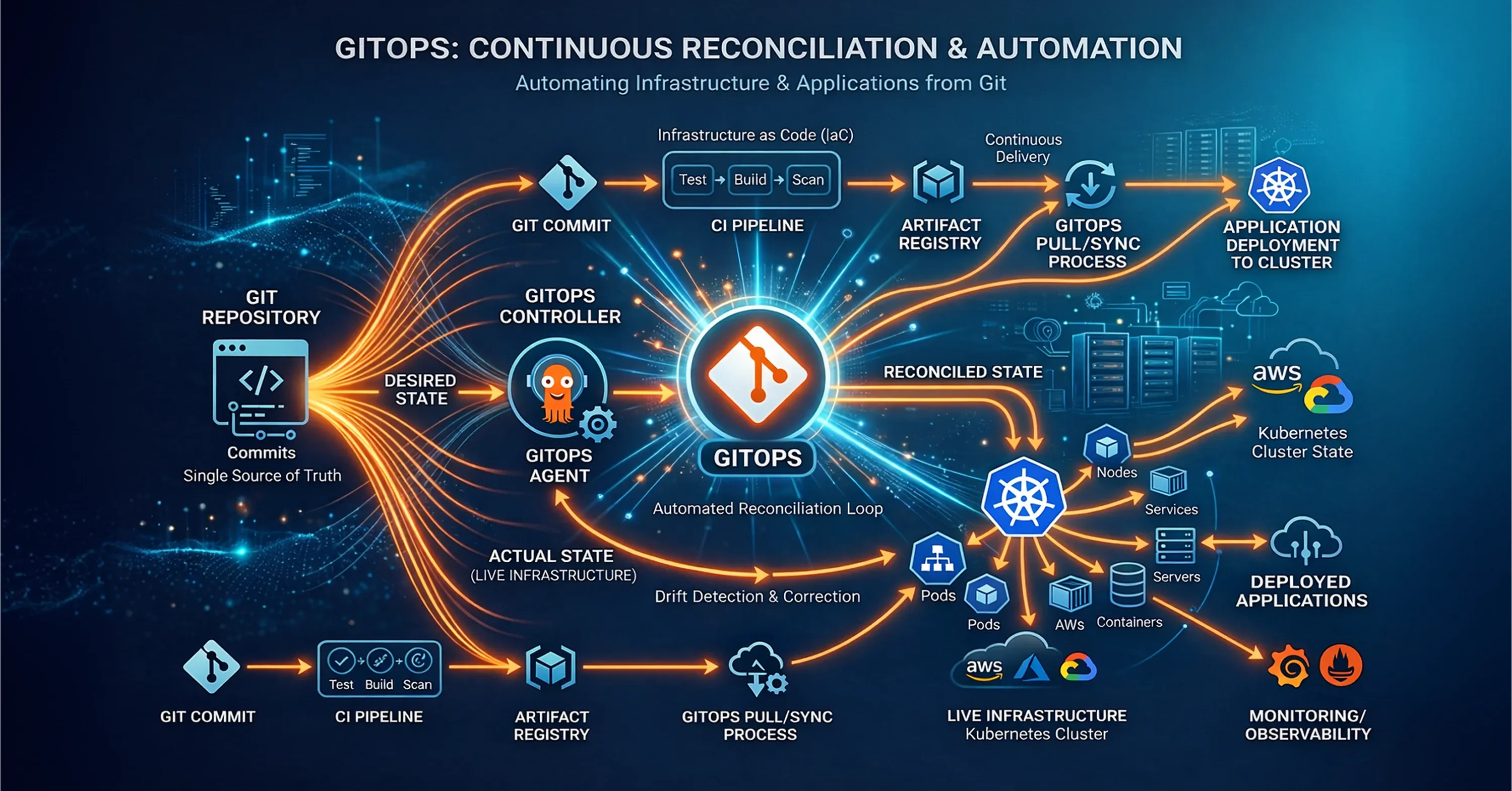
Knowing drift exists is not enough; something must reconcile it. GitOps treats the Git repository as the single source of truth, while an agent continuously pulls, plans, and applies changes until the live system matches the repo.
Implement GitOps for IaC in three moves:
-
Place all Terraform, Pulumi, or OpenTofu code in a dedicated Git branch
-
Use tools like Argo CD, Flux, or Atlantis to watch the repo and trigger plan/apply pipelines
-
Require every change to go through pull requests with automated tests and policy checks
In practice, GitOps eliminates manual console edits because any deviation is overwritten by the agent. This bridges the gap between sprawl and self-healing, paving the way for automated recovery.
GitOps takeaway: continuous reconciliation turns drift from a passive report into an active fix.
Self-Healing Infrastructure Recovered a Critical Service in Under Two Minutes
A SaaS analytics firm migrated 160 Terraform workspaces to Flux. When an engineer mistakenly deleted a production load balancer, the Flux agent noticed the missing resource and recreated it in 90 seconds, limiting downtime to a single failed request. To understand how robust automation, guardrails, and observability connect with these practices, check out Tech-Driven DevOps: How Automation is Changing Deployment.
Mutable vs. Immutable Infrastructure - Why the Debate Is Fading
Cloud architecture once revolved around whether systems should be mutable (changed in place) or immutable (replaced on every update). Mutable environments offer flexibility but accumulate hidden drift, while immutable models improve consistency at the cost of operational overhead.
Infrastructure as Code - especially terraform infrastructure as code - changes the equation. When environments are defined declaratively and continuously reconciled through GitOps, what matters is not how resources change but whether they remain aligned with the approved state.
In modern IaC platforms:
-
Manual mutations surface as drift
-
Git-driven changes become the only trusted path
-
Rollbacks are predictable regardless of replacement or modification
-
Auditability is built into the workflow
The industry is therefore moving beyond mutable versus immutable toward a new goal: infrastructure that is compliant by design and continuously convergent.
Even technically mutable systems behave operationally as immutable because any unauthorized change is detected and corrected automatically.
Compliant by Design: Policy, Governance, and FinOps as Code
Security teams used to bolt checks onto release gates, often blocking releases. Today, Policy as Code frameworks like Open Policy Agent (OPA), HashiCorp Sentinel, and Regula embed rules directly in the CI pipeline.
Key governance controls to codify:
-
Tagging and labeling standards for chargeback
-
Allowed regions, VM sizes, and container base images
-
Encryption and network isolation requirements
For FinOps, add cost lenses:
-
Estimate spend during plan using infracost or Infracost Cloud
-
Fail builds that exceed budgets
-
Surface cheaper instance types in pull-request comments
This makes every merge a compliance and cost checkpoint, shifting reviews left and preventing “rogue” resources.
If you want an in-depth, hands-on approach to automated pipelines and embedded security, see Balancing Cloud Computing and Cloud Security: Best Practices.
Disaster Recovery and the Road to Self-Healing
Because IaC stores the full environment as code, recreating entire regions becomes a deterministic process. Extend the number of scenarios:
-
Replicate state back-ups to a second region
-
Version secrets and database snapshots in the recovery code path
-
Keep a “chaos” environment to test failover weekly
Add automated remediation:
-
Detect outage via observability signals (latency spike, 5xx errors)
-
Trigger GitOps agent to apply a pre-approved DR plan (e.g., deploy into us-west-2)
-
Shift traffic with DNS or load-balancer failover policies
The vision: the system heals itself, no 3 a.m. calls required.
If you’re interested in deeper guidance on automating disaster recovery and rapid root cause analysis, read Cloud Support: How Managed DevOps Keeps Your Business Online 24/7..
AI SREs: Refactoring Legacy Templates into Modern Modules
Large language models can already parse legacy ARM or CloudFormation into Terraform 1.8 HCL, reducing manual refactor time.
Practical workflow:
-
Feed the template and desired module style guide into the LLM
-
Validate generated code with terraform validate and policy checks
-
Run cost estimation and security scans before merging
This AI assistance aligns with Gartner analyst Paul Delory’s comment that developers should not need to know Terraform exists. By abstracting the heavy lifting, LLM copilots free engineers to focus on application logic.
A leading provider of managed IT services already wraps such LLM refactors into its onboarding service, letting enterprises modernize hundreds of templates in weeks rather than quarters.
Observability as Code Closes the Loop
Self-healing only works when the system sees itself. Observability as Code provisions metrics, logs, and traces in the same repo as infrastructure.
Steps to implement:
-
Create Terraform/Pulumi modules that instrument new services with OpenTelemetry
-
Auto-generate dashboards for every microservice
-
Treat alert thresholds as code, reviewed in pull requests
Benefits:
-
Consistent monitoring coverage
-
Drift detection for telemetry resources themselves
-
Faster Mean Time to Detect (MTTD) and Repair (MTTR)
For a deeper understanding of how observability and feedback loops drive resilient cloud operations, refer to Top Cloud Sources Every Business Should Know.
Observability as Code provides the signals that GitOps uses to drive remediation, making the entire system reflexive.
Day 2 Operations: Sustaining Infrastructure Beyond Provisioning
Many organizations still treat Infrastructure as Code as a Day 1 milestone - the successful deployment of cloud resources. But real operational maturity begins after go-live.
Cloud providers release updates. Modules evolve. APIs deprecate. Security advisories require urgent patching. Costs slowly creep upward. Without structured maintenance, even well-designed Terraform or OpenTofu stacks accumulate hidden risk.
Sustainable IaC adoption requires disciplined Day 2 operations across three critical areas.
Provider & Module Lifecycle: Preventing Version Debt
Every IaC stack depends on provider versions, reusable modules, and core runtime updates. When upgrades are postponed, organizations accumulate “version debt,” making future migrations risky and disruptive.
Mature teams implement:
-
Version pinning with controlled upgrade paths
-
Scheduled provider and module review cycles
-
Automated dependency scanning in CI pipelines
-
Testing upgrades in non-production workspaces before rollout
Incremental upgrades prevent infrastructure code from becoming legacy.
State File Governance: Protecting the Infrastructure “Brain”
The state file maps declared infrastructure to real-world resources. If lost, corrupted, or exposed, recovery becomes complex and sometimes costly.
Enterprise-grade governance includes:
-
Encrypted remote backends
-
Strict IAM access control
-
State locking to prevent concurrent corruption
-
Versioning and automated backup replication
Treating the state file as a regulated asset significantly reduces operational risk.
The Clean-Up Protocol: Eliminating Zombie Resources
Temporary environments enable experimentation - but without automated decommissioning, they accumulate and drive silent cost leakage.
A Clean-Up Protocol introduces:
-
Mandatory TTL (Time-to-Live) tagging for sandbox stacks
-
Scheduled scans for expired environments
-
Automated destroy workflows with approval gates
This ensures innovation does not translate into uncontrolled cloud sprawl.
Provisioning infrastructure is increasingly automated. Maintaining it securely, cost-efficiently, and without disruption is where true IaC maturity - and real MSP differentiation - emerges.
What Is Infrastructure as Code (IaC) and How Does It Automate Cloud Deployments?
Infrastructure as Code (IaC) automates cloud deployments by storing every resource - networks, servers, policies, and even dashboards - as version-controlled text files. When paired with GitOps agents, the code becomes the desired state, drift is detected and reconciled automatically, governance rules block risky changes before they ship, and disaster recovery can recreate entire regions in minutes. The result is a self-healing, cost-governed cloud that scales safely without manual console work.
Conclusion
IaC has evolved from simple provisioning scripts to a comprehensive framework that manages the full cloud lifecycle - drift remediation, cost governance, disaster recovery, and even self-healing. When combined with GitOps, Policy as Code, Observability as Code, and AI-powered refactoring, it forms the operational backbone for modern enterprises. Adopt these practices incrementally, measure drift debt and recovery times, and watch your cloud deployments become safer, faster, and far easier to manage.